Length is great, but the phrase from which it is derived is complicated, and you've got a special character ('$') standing in for an 'S'. Are you going to remember that whole phrase? Are you going to remember where you swapped in the weird character? Was it a zero for an 'O'? or a one for an 'L'? Are you going to remember the date format? Was it month/day or day/month? With/without leading 0's? Were there slashes? Also, the continual alternation between upper and lowercase, particularly over such a long string, is going to make it ripe for typos.
Already dissected earlier, but the main problems are length, weird character, unnecessary abbreviations, and alternating upper/lower case characters.
Length is great, which makes all the convolution unnecessary. Was it Russian
whores or Russian
hookers? Was it mattress or bed? Was it "Donald Trump" or just "Trump?" And again, with the unnecessary, out-of-place weird character.
Right, and that's the problem. Sysadmins are trying to defend us from humans trying to "guess" our passwords. "Don't use your pet's name! Don't use your street name!"
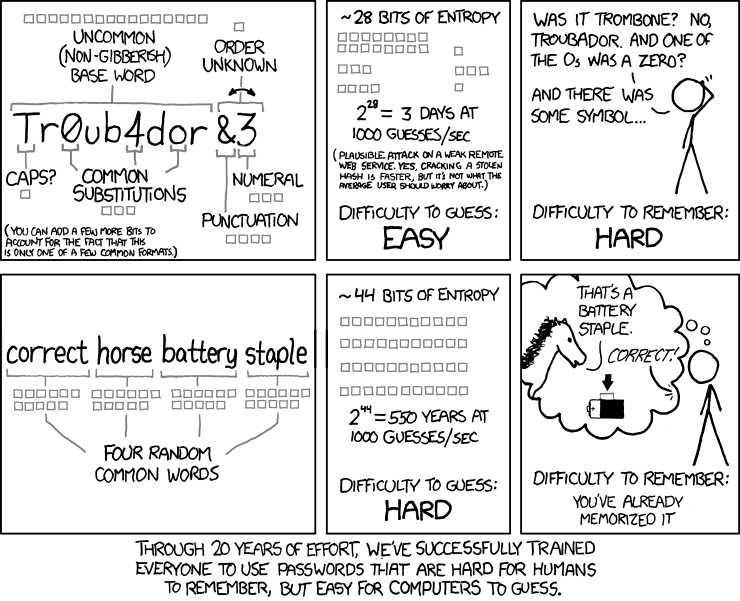
Trouble is, nobody's trying to guess your password. Hackers get a hold of a hashed password file, and leverage networks of load-sharing computers to brute-force your password. They're trying every combination of every possible character. Expanding the pool of potential characters helps some, but not as much as increasing the length. 74^10 (10 character password, using only numbers and upper/lowercase letters) is much bigger than 93^8 (8 character password, all numbers, upper/lowercase letters, punctuation, and common special characters).
They don't do dictionary attacks anymore (well, they might start out with that, since it's trivially fast now), but if they can't find it in their pool of common passwords, they just start going through every combination, getting longer and longer, until they find a match. They can try every combination of 2 characters in milliseconds. Same for 3 characters. 4 characters, they can exhaust the problem space in seconds/minutes. But it takes exponentially longer with each added character.
10 characters should be a bare-minimum length for passwords, but even those can be cracked fairly quickly with sufficient computing power. 14 characters or longer takes so long that hackers will give up and move on to the next one (at least, with current computing power).
So yes, it's primarily the length that matters.
Right. But "CorrectHorseBatteryStaple" is far easier to remember than "AM@NeT0Be1nSoIBeIWiHaAnBe." And your pattern of "Person, Place, Thing and Date" is even better still, in my opinion, because instead of having to remember 4 random words, you can use a particular event that is meaningful to you (i.e., "SchlenkerlaDenverBirthdayJune091980", or an anniversary, your graduation, whatever).
I do the same thing, but not because it's easy, because my employer's password rules have archaic requirements. Ironically, using the actual phrase itself would be far more secure than the shorter, more convoluted hash I'm forced to derive from it.
Removing the requirement to maintain a "consistent means" of converting a phrase into a password can only make the passwords both easier to remember (i.e., ditch the "means" of conversion altogether) and more secure (because you're using the longer actual phrase, rather than a shortened hash of it).
It's not. It's plenty long. But it's hard to remember. Not the phrase, that's easy (I already remember it), but the weird abbreviations and substitutions you're doing. Ironically, if you ditched the shortening and substitutions, it would be a FAR MORE secure password (wrapped in code tags to keep BBcode from inserting a space):
Code:
Amanneedstobelieveinsomething,IbelieveIwillhaveanotherbeer.
Heck, you could chop off the second half altogether and it would still be almost as secure as the first one (which, at 26 characters, far exceeds anything crackable with current technology). That is, "Amanneedstobelieveinsomething" is an exceptionally secure password, and much easier to remember and input correctly than your version.
The phrase is, yes, for sure. It's the "convolution" rules that are the problem.
That's entirely my point: There doesn't NEED to be a "twist." That's old school password thinking. Humans aren't guessing passwords anymore. We've moved past that. It's computers, throwing every possible combination of every possible character at your password's hash until it gets a match.